WireGuard Automatic Key Rotation With Pro Custodibus
One of the exciting new features of Pro Custodibus is its automatic WireGuard key-rotation policies. These policies allow you to frequently rotate the preshared keys used by your WireGuard connections, significantly limiting the risk that stolen keys will adversely impact your organization.
Why Rotate Keys
Regular key rotation is a critical component of most every security system, as it allows you to limit the damage of key theft. If an adversary sneaks through all the system’s other defenses, and steals the system’s secret keys, the adversary will be able to access the system through the “front door” until you rotate the system’s keys.
If you know an adversary has broken into a system, rotating the system’s keys would be one of the first things you do to cut off their access. But unfortunately, you often don’t know about the break-in until months afterward — like 15 months in the case of the Solar Winds breach, 5 months in the Equifax breach, or 4 years with the original Marriott breach.
That’s why regular key rotation is standard operating procedure for most security systems — to proactively cut off access to an undiscovered breach.
Why Automatic Rotation
Most organizations have security policies that require all secrets to be rotated on a regular basis. But because rotating secrets is often a painful, laborious process, this “regular basis” is usually yearly (or longer). The upside of such a policy is that it ensures an adversary won’t have surreptitious access to a system for longer than a year — but the downside is that it allows access for up to a year.
However, when you have the capability to rotate keys automatically, with no manual action necessary, you can rotate keys much more often. With manual rotation, if an organization had a policy that required keys to be rotated as often as monthly, it would be the source of much griping and frequent support calls. But with automatic rotation, monthly rotation is easy and pain-free.
In fact, with automatic rotation, a rotation interval of much, much less is suddenly practical. You can rotate keys weekly, daily, hourly — or even every few minutes! Instead of worrying about how long you have to set the rotation interval in order to stave off revolt from your users and sysadmins, you can can just worry about how short you should make the interval to prevent a stolen key from actually doing real damage.
Why Preshared Keys
With WireGuard, you can supplement the security of the public-key pairs that form the basis of WireGuard’s authentication and encryption mechanism with a secret symmetric key, shared by both sides of an individual connection. This is known as a preshared key. While a single key pair is tied to each WireGuard interface — so the same key pair will be used by each of the connections to all the other peers connected to the interface — each connection has its own distinct preshared key.
This can make WireGuard public-key pairs tricky to rotate, since each key change must be coordinated across all the different peers connected to the same interface. However, since each preshared key is used only by a single connection, rotating it is much simpler — you only have to update the key on its two endpoints.
How To Set Up Automatic Rotation
Setting up automatic key rotation with Pro Custodibus is easy! All you have to do is make sure you have the Pro Custodibus agent running on both sides of each connection you want to rotate, and then create a simple key-rotation policy through the Pro Custodibus UI.
An example of this was covered in the WireGuard MFA Guide, but let me show off two common scenarios here: first, where we have a bunch of point-to-point connections, like a bunch of app servers that connect to other infrastructure over WireGuard, like to a database, log system, mail server, and auth server; and second, a central hub (like a traditional VPN or jump host) that connects some internal infrastructure at a site to remote end-user devices.
Point to Point
If you have a bunch of servers with individual WireGuard connections between them, you can set up a single key-rotation policy to cover them all. For example, say we have a cluster of individual app servers connected point-to-point to various other pieces of infrastructure through WireGuard, like to a database, log system, mail server, and auth server:

The first thing to do is make sure that all of these hosts have a Pro Custodibus agent running on them.
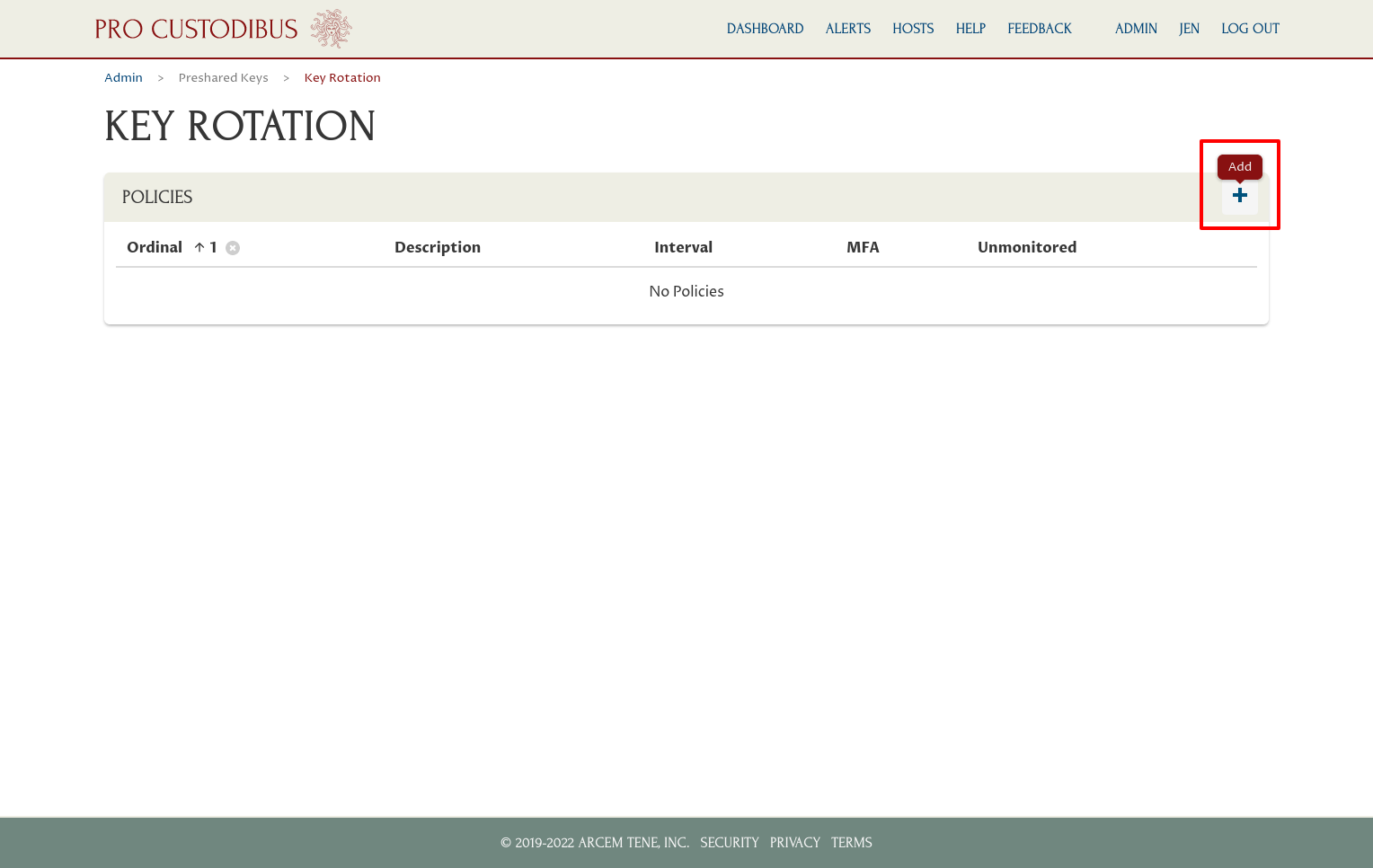
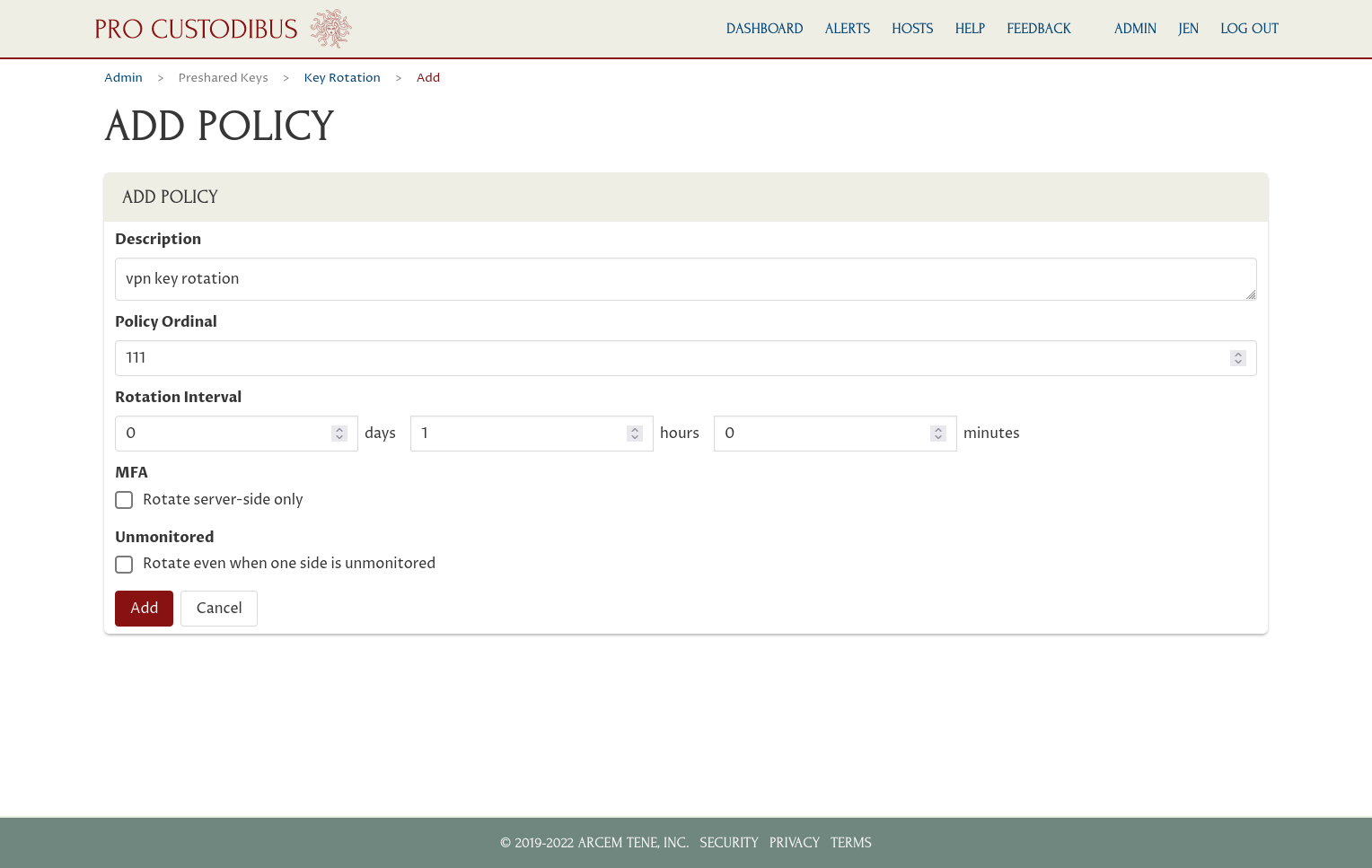
Once you’ve done that, you can navigate to the Admin section of the Pro Custodibus UI, and from there to the Key Rotation Policies page. On the Policies panel of that page, click the Add icon to create a new policy:
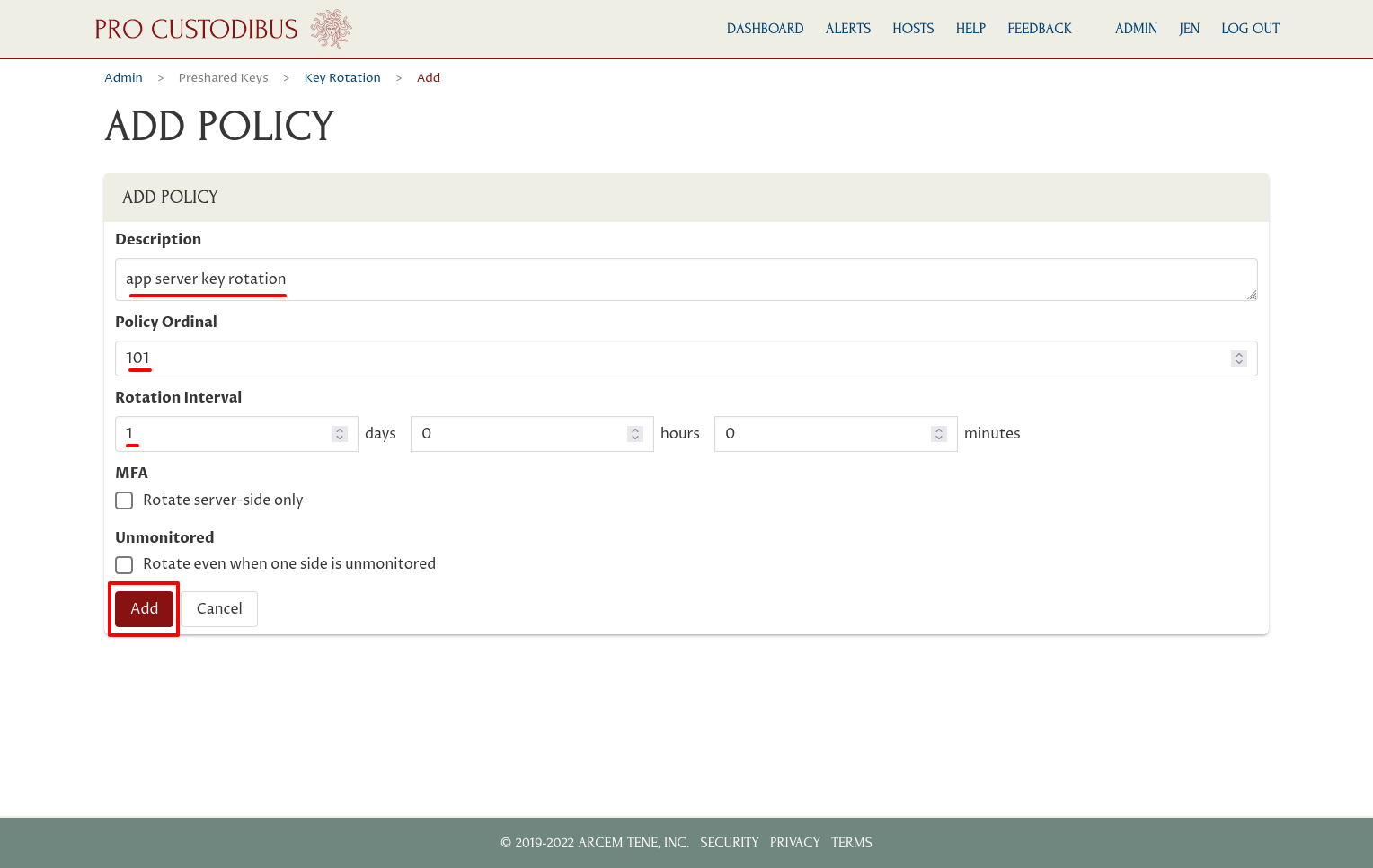
Then configure some of the basic details of the policy:
- Description
-
A human-readable description for the policy.
- Policy Ordinal
-
Only one policy can apply to a given connection between two peers — the policy with the lowest ordinal number “wins”.
- Rotation Interval
-
Interval over which to rotate the keys (can be as short as every 5 minutes).
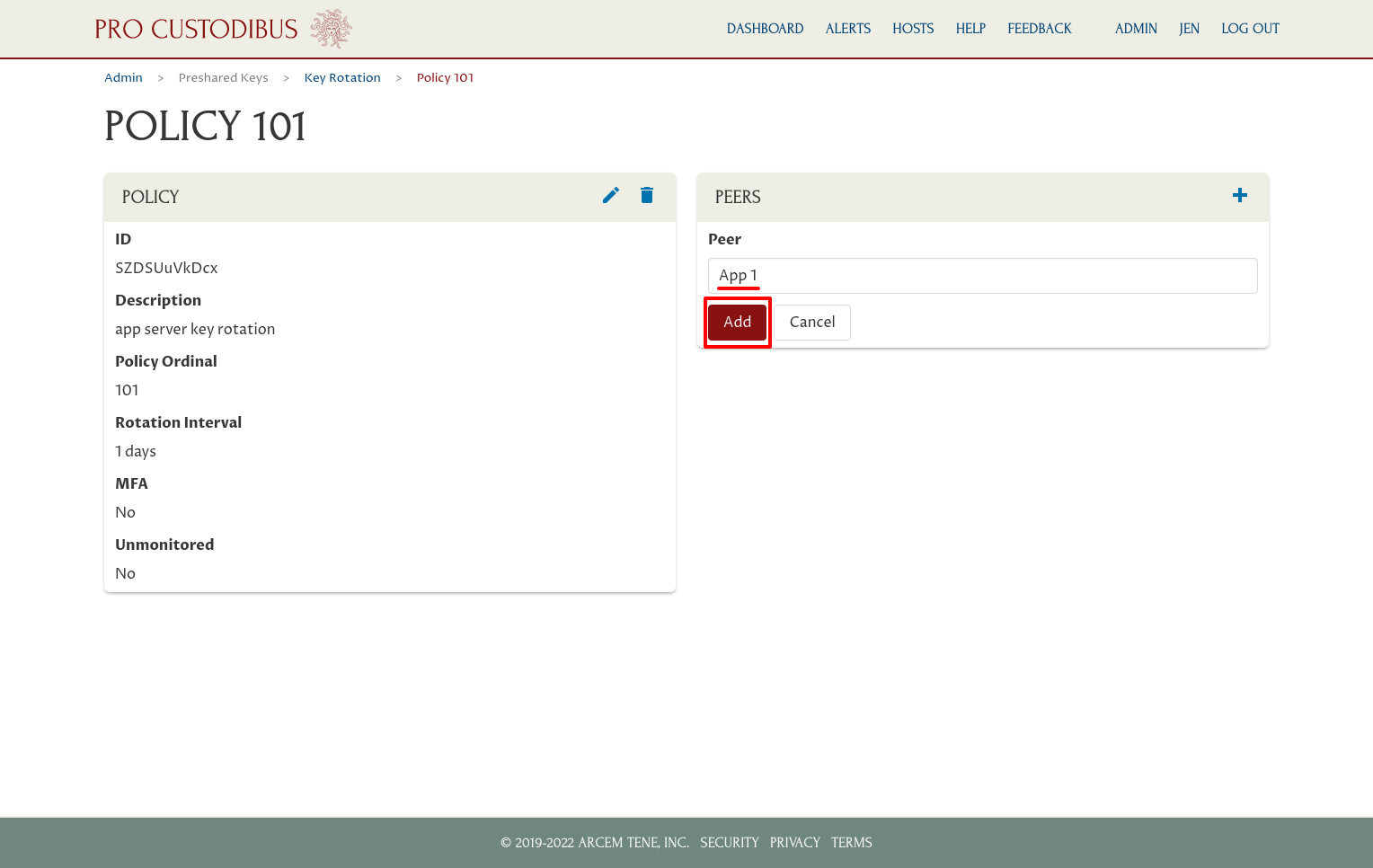
Once the policy had been created, you add peers to the policy by clicking the Add icon in its Peers panel:
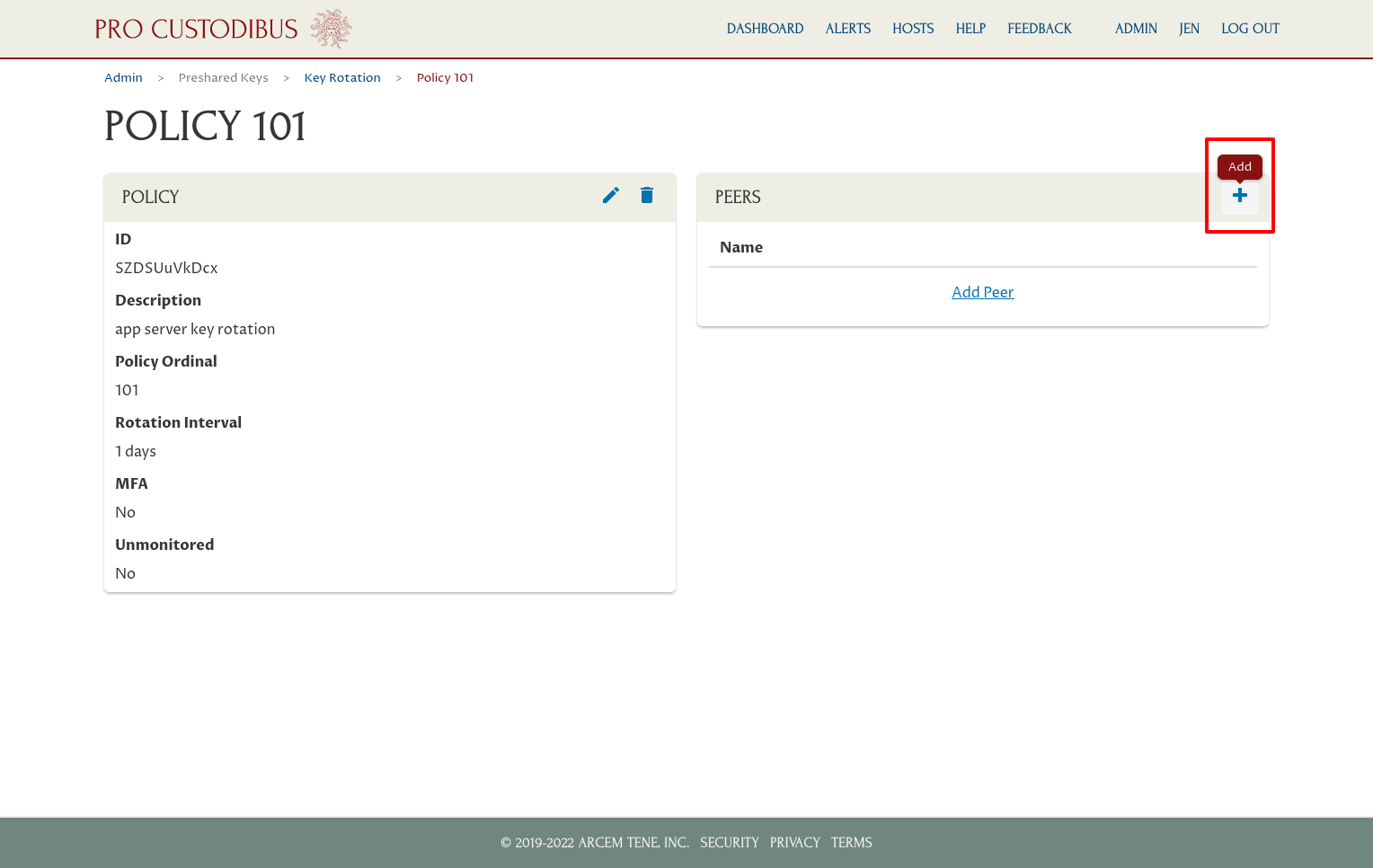
Select a peer to add (begin typing the peer’s name to filter the selectable list), then click the Add button:
In this case, we want to add our four app servers:
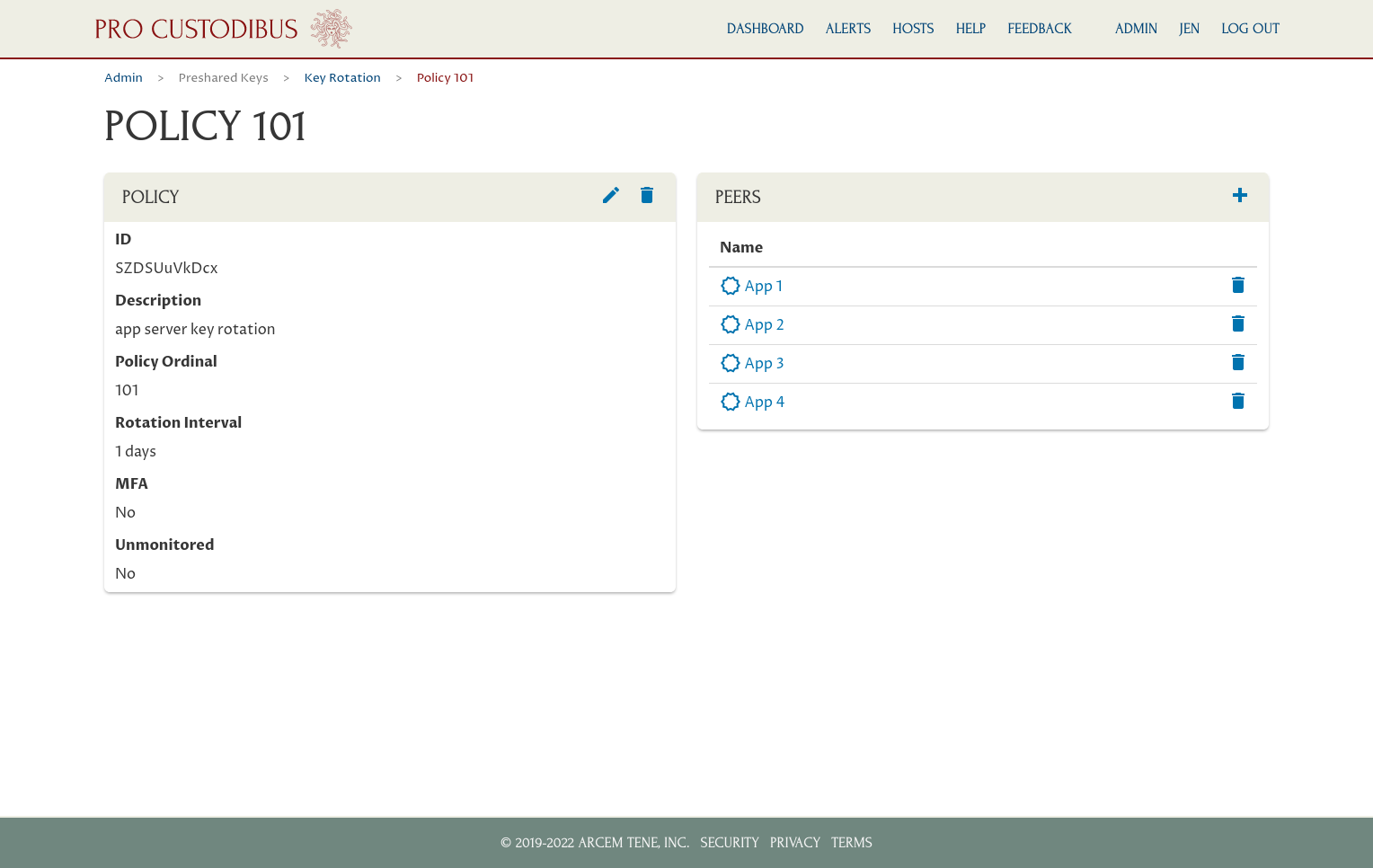
This new policy will apply to all WireGuard connections of these peers (or at least all that have the Pro Custodibus agent installed on both sides of the connection). The preshared key used by each connection will be rotated automatically once a day — so if an adversary steals the WireGuard keys for one the app servers (ie the private key of the peer’s key pair and all the preshared keys used by its connections) — or the WireGuard keys for any of the other servers to which the app servers are connected — the adversary will have at most 24 hours to use the keys.
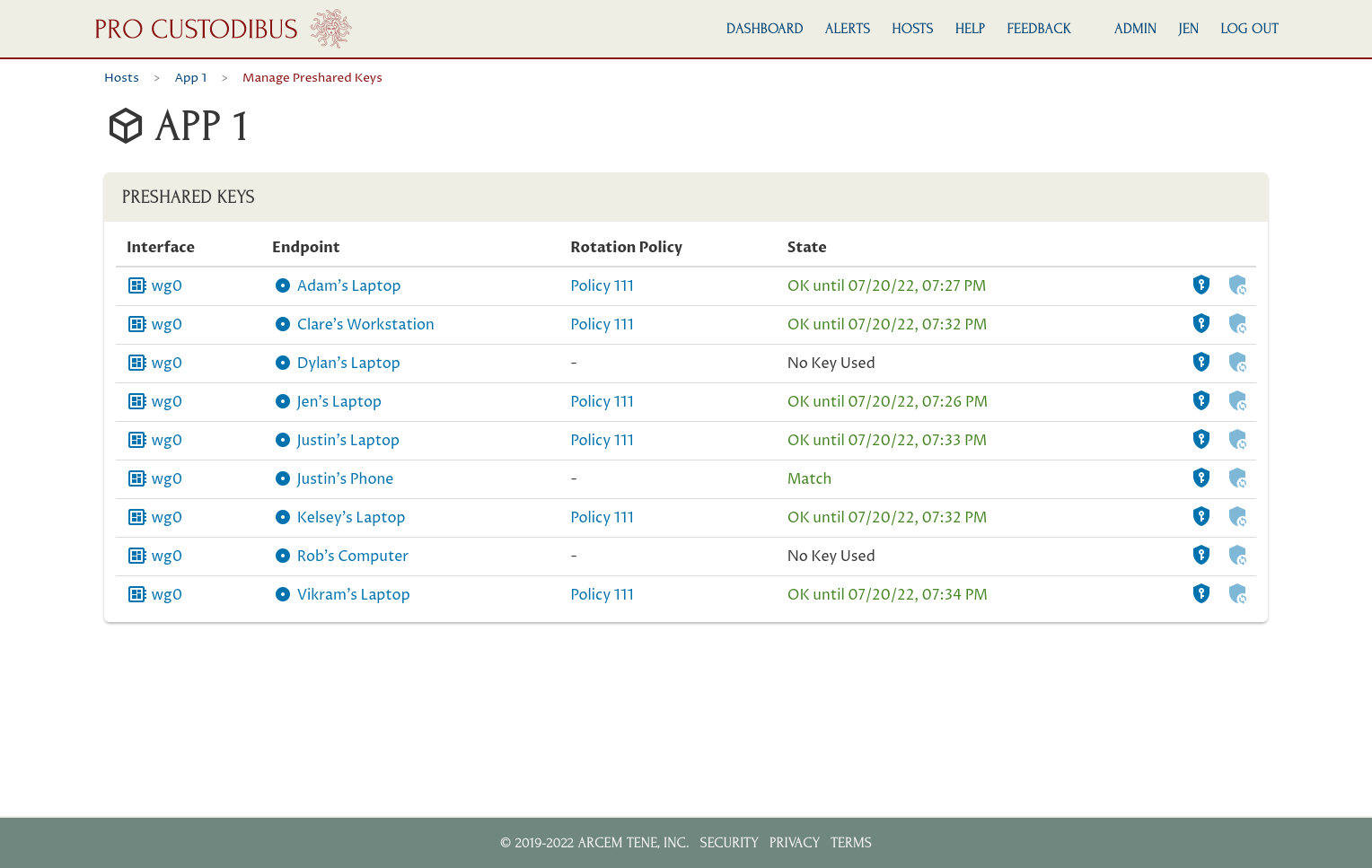
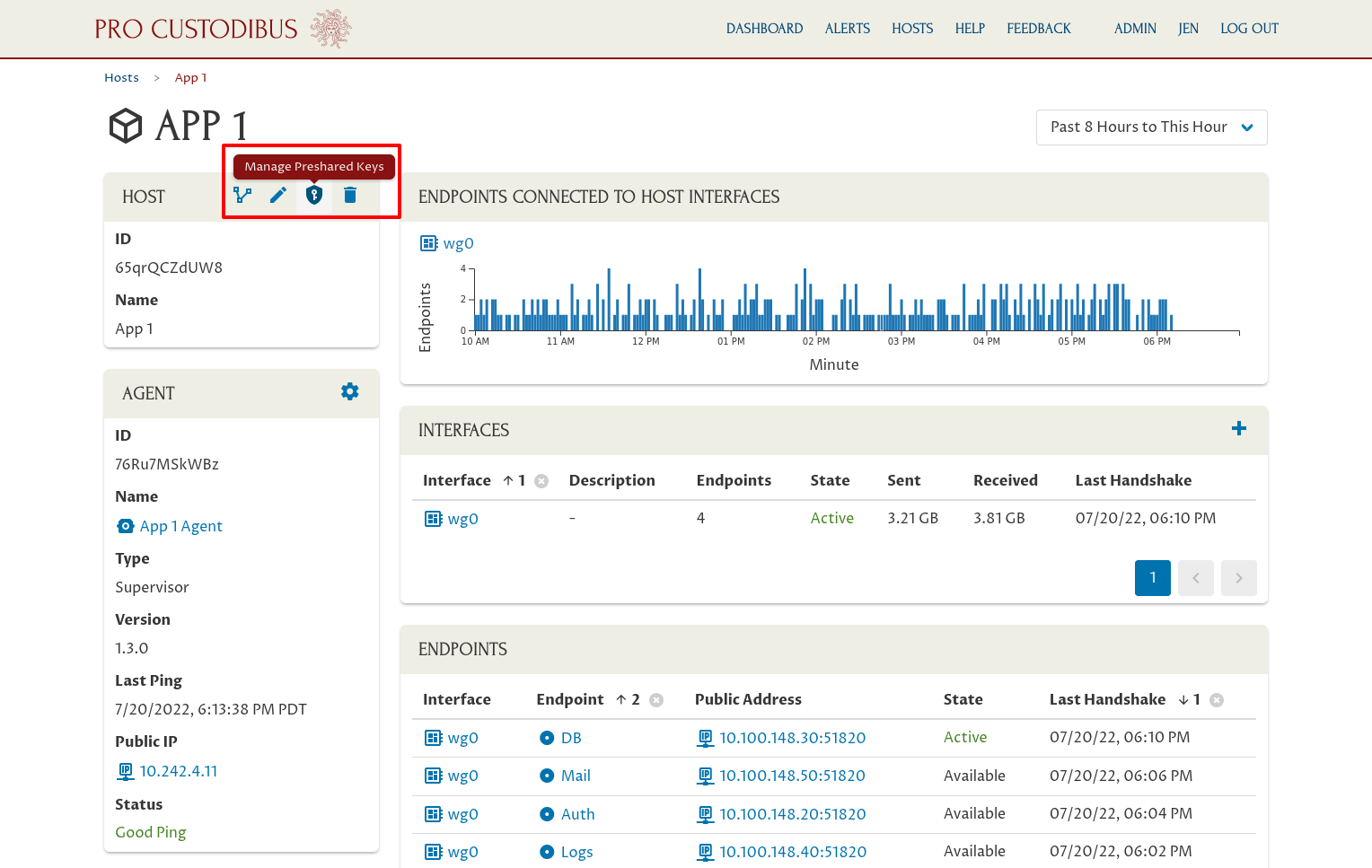
You can check on the rotation state of a particular host by navigating to it, and clicking on the Manage Preshared Keys icon of its Host panel:
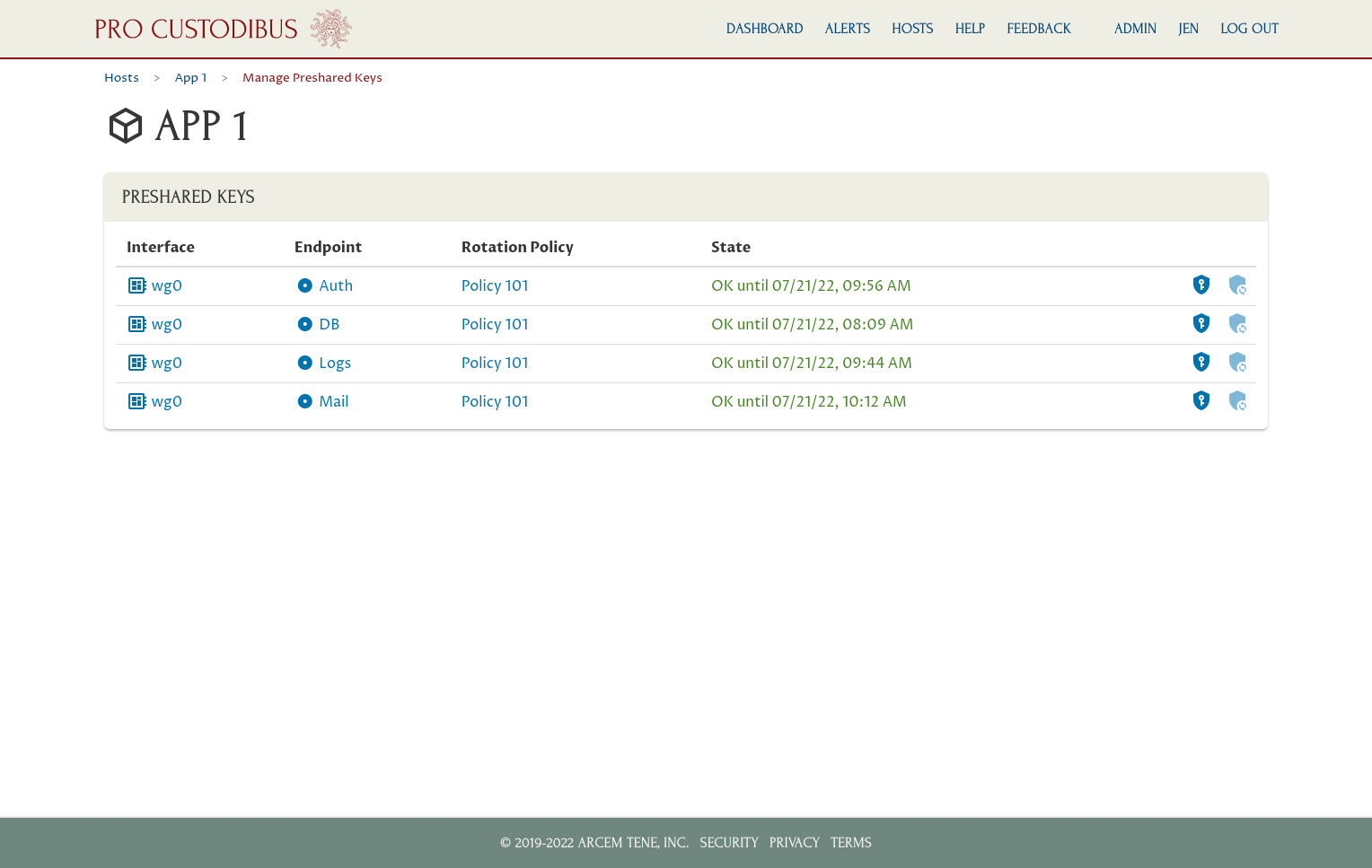
This will show when the preshared key for each of its connections is due to be rotated, and which key-rotation applies to each:
Hub and Spoke
If you have one server that a number of other WireGuard clients connect to, you can also set up a key-rotation policy for that one server, covering all of the connections to that server. For example, say we have a bunch of user devices that are connected to a central VPN server, through which those user devices can access some internal site remotely:

To set up key rotation for all those connections, first make sure that the VPN server and all of its connected hosts (or at least the ones whose key you want to rotate) have a Pro Custodibus agent running on them.
Once you do that, you can create simple a key-rotation policy just like the first example. For this particular policy, we’ll set the rotation interval to 1 hour:
And we only need to add the VPN server’s peer identity to the policy’s peers list:
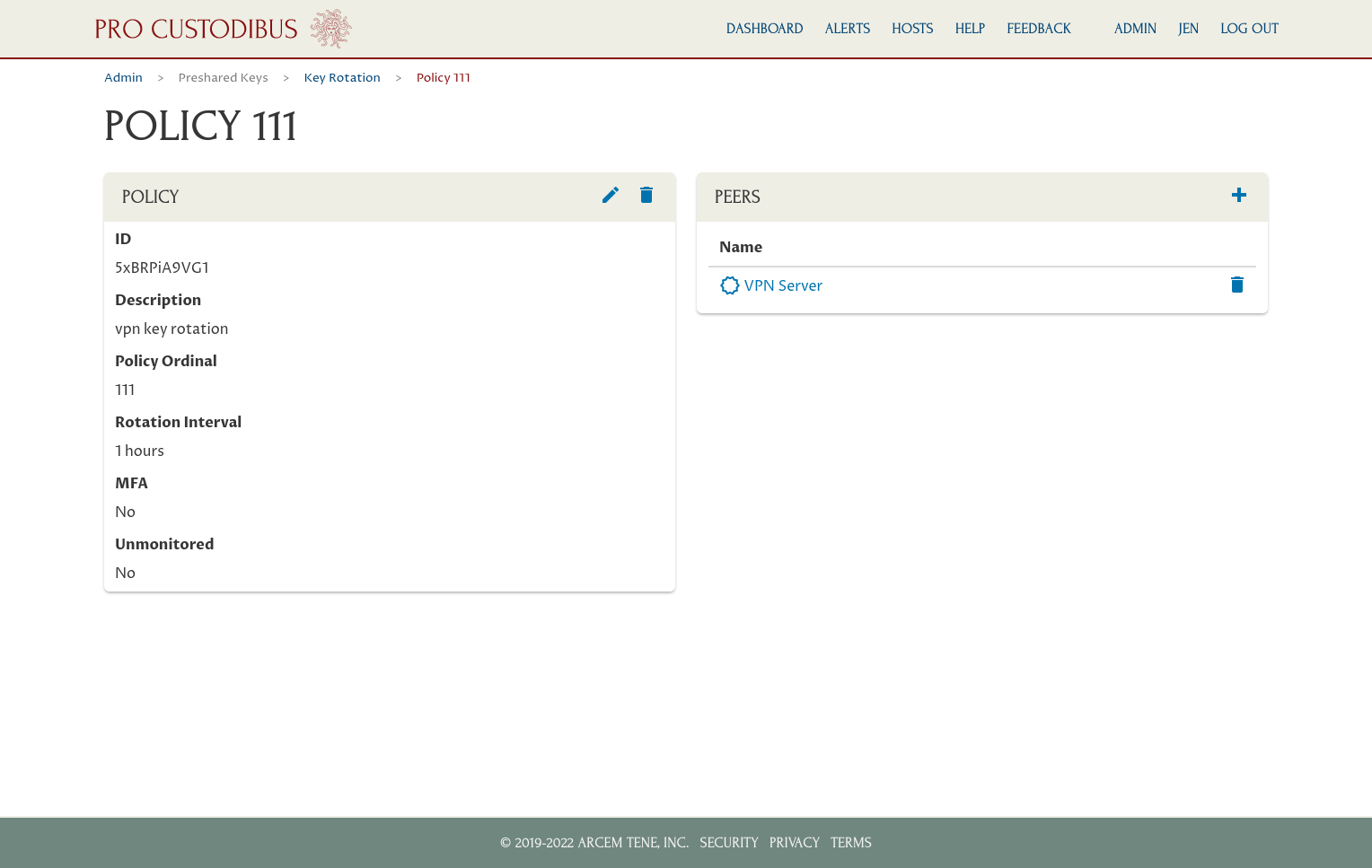
This policy will apply to all connections to the VPN server from clients that also have the Pro Custodibus agent installed on them. The preshared key of each of these connections will be rotated once an hour. If an adversary steals the keys from one of these clients, the adversary will have at most one hour to use the keys.
The Manage Preshared Keys page for the VPN server will show the connections to which the policy applies (clients that aren’t configured to use the Pro Custodibus agent aren’t included in the policy), and when the key for each connection is due to be rotated: